Check Point® Software Technologies Ltd.(link is external) announced that U.S. News & World Report has named the company among its 2025-2026 list of Best Companies to Work For(link is external).
According to Forrester research, of 40 university computer science programs in the US, not one requires students to take secure coding or secure application design courses. That piece of the cyber skills gap means such training is often left up to individual teams.
Developers are not, and should not be expected to be, security experts.
Start with New Report: Speed and Security Are Both Possible in Software Development - Part 1
But to make DevSecOps more effective and address both the speed and security pressures, development and security teams need to understand each other better. For developers, that means understanding how applications can be exploited — the OWASP Top 10 is a good start.
ESG listed other elements of the most effective AppSec programs, several of which include better security awareness for developers. They include:
■ Application security best practices are formally documented.
■ Application security training is included as part of the ongoing development security training program.
■ Development managers are responsible for communicating best practices to developers.
■ A high percentage of developers participate in formal application security training programs.
■ Security issue introduction is tracked for individual development teams.
Then there is the technology piece, a major part of which is security testing tools.
Tools are crucial to finding design flaws, vulnerabilities in code and open source defects and licensing conflicts. Most organizations use multiple tools, but some of them have gone overboard — way overboard.
ESG reported(link is external) more than a year ago that organizations on average run 25 to 49 security tools from up to 10 different vendors. There's an industry term for it — "tool sprawl." And it can slow productivity and lead to higher overall costs — the very things a good mix of security tools should help development teams avoid.
Analysts like Forrester and 451 Research have reported on tool sprawl in the past year, noting that as many as 40% of organizations admit that their development teams are so overwhelmed by security alerts that they can't respond to at least 25% of them. Indeed, when security alerts are so constant, they become background "noise" and are ignored — the exact opposite of the intent.
Survey respondents are aware of the problem. "Nearly one-third of organizations are … planning future investment to consolidate and simplify their tools proliferation," the report said.
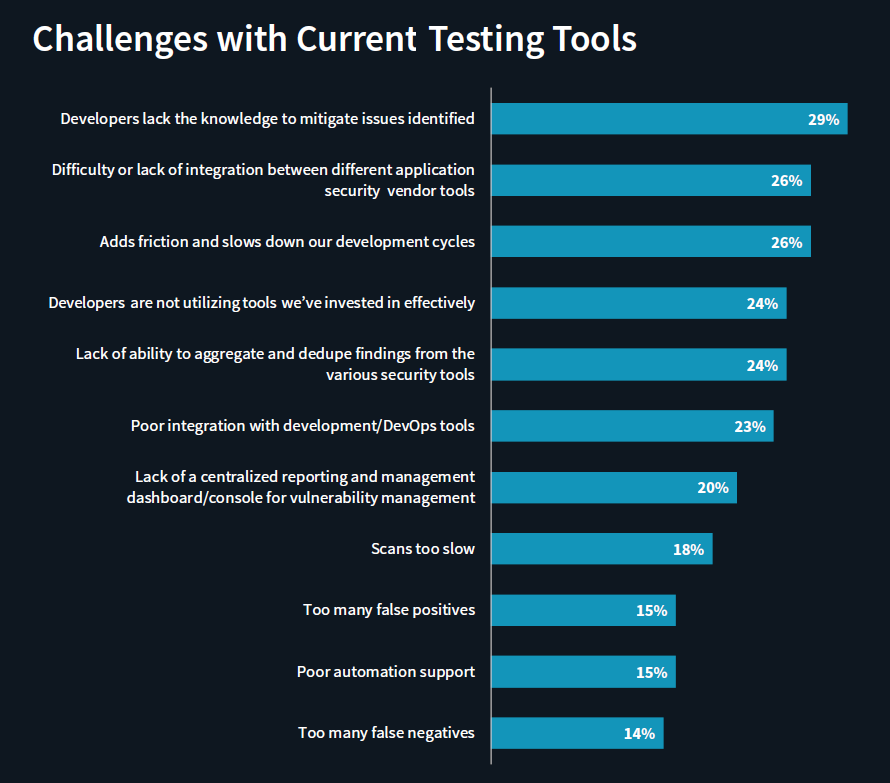
So, clearly one part of the solution is DevOps integration — finding the right mix of tools that can work together and are easy for developers to use. ESG found that, for organizations seeking to improve the security of their software, "the most common challenge with their current tools is that their developers lack the knowledge to (mitigate identified security issues)."
The other part is automation. "Most believe that automating application security testing throughout the SDLC can make the biggest impact on the success of their program. DevOps integration reduces friction and shifts security further left, helping organizations identify security issues sooner," the report said.
The obvious goal is to build both security and speed into the SDLC. And based on the survey results, organizations are willing to invest to achieve that. More than half reported plans to "significantly increase spending on application security over the prior year."
Which means there is at least a chance that at some point in the future, the market will indeed get software-powered products that are the latest, greatest — and also the safest.
Industry News
Postman announced new capabilities that make it dramatically easier to design, test, deploy, and monitor AI agents and the APIs they rely on.
Opsera announced the expansion of its partnership with Databricks.
Postman announced Agent Mode, an AI-native assistant that delivers real productivity gains across the entire API lifecycle.
Progress Software announced the Q2 2025 release of Progress® Telerik® and Progress® Kendo UI®, the .NET and JavaScript UI libraries for modern application development.
Voltage Park announced the launch of its managed Kubernetes service.
Cobalt announced a set of powerful product enhancements within the Cobalt Offensive Security Platform aimed at helping customers scale security testing with greater clarity, automation, and control.
LambdaTest announced its partnership with Assembla, a cloud-based platform for version control and project management.
Salt Security unveiled Salt Illuminate, a platform that redefines how organizations adopt API security.
Workday announced a new unified, AI developer toolset to bring the power of Workday Illuminate directly into the hands of customer and partner developers, enabling them to easily customize and connect AI apps and agents on the Workday platform.
Pegasystems introduced Pega Agentic Process Fabric™, a service that orchestrates all AI agents and systems across an open agentic network for more reliable and accurate automation.
Fivetran announced that its Connector SDK now supports custom connectors for any data source.
Copado announced that Copado Robotic Testing is available in AWS Marketplace, a digital catalog with thousands of software listings from independent software vendors that make it easy to find, test, buy, and deploy software that runs on Amazon Web Services (AWS).
Check Point® Software Technologies Ltd.(link is external) announced major advancements to its family of Quantum Force Security Gateways(link is external).
Sauce Labs announced the general availability of iOS 18 testing on its Virtual Device Cloud (VDC).




